Shopping online has continually grown in popularity, especially when it comes to tracking down that hard-to-find item, and cybercriminals have certainly taken notice. According to the Better Business Bureau (BBB), online shopping scams reported to their Scam Tracker have risen 87% since 2015. And so far in 2022, online scams remain the most reported fraud type, with losses expected to reach $380 million by year-end.
Now that the season for giving is here, cyber deals are likely flooding your inbox ... along with cybercriminal attempts to trick you out of money and your confidential information. Since we all like to get a good deal, the best way forward is to be shopping online safely.
Before you take advantage of the next online deal, take a look at these top cybersecurity tips you can follow.
- Pay attention to the URL
- Verify the security of the webpage
- Make purchases only on secure networks
- When in doubt, don't check out
Pay attention to the URL
First and foremost, it's important to recognize the anatomy of a website address (URL) to identify when something looks out of place. The image below is a sample URL with various parts of a web address called out.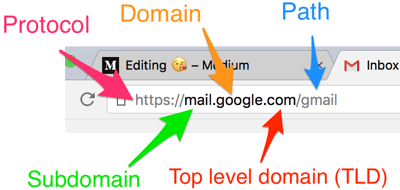 It's not always easy to spot a fake URL. Fraudulent websites can often create realistic-looking fake sites to imitate brands you are familiar with such as Amazon, PayPal, Best Buy, Google, etc. The domain will often have the letters of the brand name transposed or misspelled and additional words or numbers used out of place.
It's not always easy to spot a fake URL. Fraudulent websites can often create realistic-looking fake sites to imitate brands you are familiar with such as Amazon, PayPal, Best Buy, Google, etc. The domain will often have the letters of the brand name transposed or misspelled and additional words or numbers used out of place.
ex: amaz0n.com / gooogle.com / betsbuy.com /
Be aware that the domain is listed directly before the .com (TLD) and cannot be changed by a hacker. What hackers can do is make the subdomain reflect the correct address, and the real domain will be their fraudulent site, like this example:
https://google.com.global-source.com
In this case, global-source.com is the real domain of this URL and google.com is the subdomain masquerading as a legitimate google domain. Don't be fooled!
Verify the security of the webpage
From login to payment, ensure all web pages are secure. A secure site uses SSL (Secure Socket Layer) encryption to keep data in transit hidden from hackers. You can recognize a secure website by looking at the website protocol. It should have the HTTPS:// protocol designation rather than simply HTTP:// (excluding the "S").
It is best to assume that all HTTP websites are unsafe and should be avoided; however not all HTTPS websites are safe. This can seem confusing, but the connection type, which is the protocol, is NOT the same as a safe website. Sophisticated cybercriminals can purchase an SSL certificate (HTTPS protocol) on their fraudulent websites too. The good news is, you can check to see if that HTTPS website's SSL certificate can be trusted in just a few clicks.
Depending on your browser, the steps will differ slightly, but when using Chrome:
1. Click the padlock in the address bar to view the site info.
2. Click "Connection is secure" for details.3. Click "Certificate is valid"to view certificate details.4. Select the "Details" tab to view further certificate information.5. In the "Certificate Fields" box, scroll down and choose "Subject".6. The "Field Value" box below will reveal the comapny /issure information, which should match the expected site.
Make purchases only on secure networks
Public Wi-Fi is fine for browsing, but it's not secure enough for buying. You may be browsing for those great holiday deals while visiting your favorite coffee shop, but be careful NOT to make any purchases while using the FREE public Wi-Fi. You'll know you're using an unsecured Wi-Fi connection if you are NOT required to enter a password, agree to legal terms, or register an account.
 If you simply can't wait, make sure to turn off your Wi-Fi and switch to your cellular connection. This will establish a connection through your network carrier/ mobile provider (i.e., Verizon, AT&T, etc.) which encrypts your transferred data and uses cell towers rather than a public Wi-Fi network.
If you simply can't wait, make sure to turn off your Wi-Fi and switch to your cellular connection. This will establish a connection through your network carrier/ mobile provider (i.e., Verizon, AT&T, etc.) which encrypts your transferred data and uses cell towers rather than a public Wi-Fi network.
When in doubt, don't check out
These are just a few of the best practices to ensure you are shopping online safely, but there are lots of other deceptive tactics hackers use that are worth learning about. If you are interested in learning a few more common tactics, read our blog titled:
Data Breach Prevention: 5 Common Threats To Be Aware Of
There are also many free public resources available that may be useful to bookmark for your next shopping session. Here are just a few we can recommend:
- GOOGLE Safe Browsing URL Site Status
- FBI Tip Sheet: Holiday Scams
- FTC Consumer Advice: Online Privacy and Security
Happy Online Shopping!
For more information on how to protect your sensitive company information, or ask about securing your organization from cyberthreats, email Systems Engineering at info@systemsengineering.com.






